Dear Friends, Today we will se how to use tcpdump command in CentOS 7. We will also see what is tcpdump? and how to install dcpdump in CentOS 7. So let’s start see step by step tcpdump installation and uses in CentOS 7.
We will cover these topics in this tutorial:-
- What is tcpdump?
- How to install tcpdump in CentOS 7?
- How to use tcpdunp commands in CentOS 7.
1. What is tcpdump?
Tcpdump is a common packet analyzer tool that runs under the command line. We can use it to display TCP/IP and other packets being transmitted or received over a network where computers are attached with each other.
Tcpdump can be use on most Unix operating systems like: – Linux, Solaris, FreeBSD, DragonFly BSD, NetBSD, OpenBSD, OpenWrt, macOS, HP-UX 11i, and AIX.
For more details abut tcpdump you can Click Here
2. How to install tcpdump in CentOS 7?
We can install tcpdump package in CentOS 7 using yum tool. Here I am going to install tcpdump package using yum in CentOS 7 you can see below.
[root@urclouds ~]# yum install tcpdump Loaded plugins: fastestmirror Loading mirror speeds from cached hostfile base: mirrors.piconets.webwerks.in extras: mirrors.piconets.webwerks.in updates: mirrors.piconets.webwerks.in Resolving Dependencies --> Running transaction check ---> Package tcpdump.x86_64 14:4.9.2-4.el7 will be installed --> Processing Dependency: libpcap >= 14:1.5.3-10 for package: 14:tcpdump-4.9.2-4.el7.x86_64 --> Processing Dependency: libpcap.so.1()(64bit) for package: 14:tcpdump-4.9.2-4.el7.x86_64 --> Running transaction check ---> Package libpcap.x86_64 14:1.5.3-11.el7 will be installed --> Finished Dependency Resolution Dependencies Resolved ===================================================================================================================================================================================================== Package Arch Version Repository Size Installing: tcpdump x86_64 14:4.9.2-4.el7 base 421 k Installing for dependencies: libpcap x86_64 14:1.5.3-11.el7 base 138 k Transaction Summary Install 1 Package (+1 Dependent package) Total download size: 559 k Installed size: 1.3 M Is this ok [y/d/N]: y Downloading packages: warning: /var/cache/yum/x86_64/7/base/packages/libpcap-1.5.3-11.el7.x86_64.rpm: Header V3 RSA/SHA256 Signature, key ID f4a80eb5: NOKEY ] 62 kB/s | 116 kB 00:00:07 ETA Public key for libpcap-1.5.3-11.el7.x86_64.rpm is not installed (1/2): libpcap-1.5.3-11.el7.x86_64.rpm | 138 kB 00:00:01 (2/2): tcpdump-4.9.2-4.el7.x86_64.rpm | 421 kB 00:00:03 Total 147 kB/s | 559 kB 00:00:03 Retrieving key from file:///etc/pki/rpm-gpg/RPM-GPG-KEY-CentOS-7 Importing GPG key 0xF4A80EB5: Userid : "CentOS-7 Key (CentOS 7 Official Signing Key) security@centos.org" Fingerprint: 6341 ab27 53d7 8a78 a7c2 7bb1 24c6 a8a7 f4a8 0eb5 Package : centos-release-7-5.1804.el7.centos.x86_64 (@anaconda) From : /etc/pki/rpm-gpg/RPM-GPG-KEY-CentOS-7 Is this ok [y/N]: y Running transaction check Running transaction test Transaction test succeeded Running transaction Installing : 14:libpcap-1.5.3-11.el7.x86_64 1/2 Installing : 14:tcpdump-4.9.2-4.el7.x86_64 2/2 Verifying : 14:libpcap-1.5.3-11.el7.x86_64 1/2 Verifying : 14:tcpdump-4.9.2-4.el7.x86_64 2/2 Installed: tcpdump.x86_64 14:4.9.2-4.el7 Dependency Installed: libpcap.x86_64 14:1.5.3-11.el7 Complete! [root@urclouds ~]#
You can see in above screen output we have successfully installed tcpdump package in CentOS 7. Now we can use tcpdump command in CentOS 7.
3. How to use tcpdump command in CentOS 7?
Now I am going to show you tcpdump command with example so that you can understand better uses of tcpdump command in CentOS 7. So let’s start and see lot’s of tcpdump commands example step by steps.
Packets capturing with a specific interface
If we run the tcpdump command without any options then it will capture packets on all the interfaces, but if you want to capture packets with specific interface then you must use -i option. Like below: –
Tcpdump commands will be this ” tcpdump -i <interface-name>
[root@urclouds ~]# tcpdump -i enp0s3 tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes 21:27:03.845404 IP urclouds.ssh > N-CNU4219HCM.56279: Flags [P.], seq 3239135489:3239135697, ack 1570297340, win 269, length 208 21:27:03.846147 IP N-CNU4219HCM.56279 > urclouds.ssh: Flags [.], ack 208, win 547, length 0 21:27:03.846214 IP urclouds.44618 > gateway.domain: 7356+ PTR? 139.43.168.192.in-addr.arpa. (45) 21:27:04.001337 ARP, Reply gateway is-at 72:3a:51:45:0e:d0 (oui Unknown), length 46 21:27:04.032719 IP gateway.domain > urclouds.44618: 7356* 1/0/0 PTR N-CNU4219HCM. (71) 21:27:04.033069 IP urclouds.57052 > gateway.domain: 37750+ PTR? 205.43.168.192.in-addr.arpa. (45) 21:27:04.035828 IP gateway.domain > urclouds.57052: 37750* 1/0/0 PTR urclouds. (67) 21:27:04.036149 IP urclouds.50642 > gateway.domain: 18719+ PTR? 1.43.168.192.in-addr.arpa. (43) 21:27:04.036280 IP urclouds.ssh > N-CNU4219HCM.56279: Flags [P.], seq 208:496, ack 1, win 269, length 288 21:27:04.038536 IP gateway.domain > urclouds.50642: 18719 NXDomain 0/0/0 (43) 21:27:04.040249 IP urclouds.ssh > N-CNU4219HCM.56279: Flags [P.], seq 496:1296, ack 1, win 269, length 800 21:27:04.040255 IP N-CNU4219HCM.56279 > urclouds.ssh: Flags [.], ack 1296, win 543, length 0 21:27:04.040404 IP urclouds.ssh > N-CNU4219HCM.56279: Flags [P.], seq 1296:1552, ack 1, win 269, length 256 21:27:04.040561 IP urclouds.ssh > N-CNU4219HCM.56279: Flags [P.], seq 1552:1712, ack 1, win 269, length 160 21:27:04.040627 IP N-CNU4219HCM.56279 > urclouds.ssh: Flags [P.], seq 1:97, ack 1552, win 542, length 96 21:27:04.040725 IP urclouds.ssh > N-CNU4219HCM.56279: Flags [P.], seq 1712:1760, ack 97, win 269, length 48 21:27:04.040821 IP N-CNU4219HCM.56279 > urclouds.ssh: Flags [P.], seq 97:161, ack 1712, win 547, length 64 21:27:04.040995 IP urclouds.ssh > N-CNU4219HCM.56279: Flags [P.], seq 1760:2256, ack 161, win 269, length 496 21:27:04.041836 IP N-CNU4219HCM.56279 > urclouds.ssh: Flags [.], ack 2256, win 545, length 0 21:27:04.041985 IP urclouds.ssh > N-CNU4219HCM.56279: Flags [P.], seq 2256:2512, ack 161, win 269, length 256 21:27:04.042166 IP urclouds.ssh > N-CNU4219HCM.56279: Flags [P.], seq 2512:2688, ack 161, win 269, length 176 21:27:04.042186 IP N-CNU4219HCM.56279 > urclouds.ssh: Flags [.], ack 2688, win 543, length 0 21:27:04.428161 IP urclouds.ssh > N-CNU4219HCM.56279: Flags [P.], seq 299952:300224, ack 2241, win 269, length 272 21:27:04.429942 IP urclouds.ssh > N-CNU4219HCM.56279: Flags [P.], seq 300224:300400, ack 2241, win 269, length 176 21:27:04.430182 IP N-CNU4219HCM.56279 > urclouds.ssh: Flags [P.], seq 2241:2305, ack 300400, win 545, length 64 ^C 2028 packets captured 2029 packets received by filter 0 packets dropped by kernel [root@urclouds ~]#
Capturing specific number of packets with specific interface
Suppose we want to capture 15 packets with specific interface then we can use below command.
Tcpdump commands will be this ” tcpdump -c 15 -i <interface-name>. You can see in below output we have successfully capture 15 packets.
[root@urclouds ~]# tcpdump -c 15 -i enp0s3 tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes 01:01:12.276512 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 1638550981:1638551189, ack 4218645468, win 269, length 208 01:01:12.277626 IP urclouds.39228 > gateway.domain: 6094+ PTR? 139.43.168.192.in-addr.arpa. (45) 01:01:12.282627 IP gateway.domain > urclouds.39228: 6094* 1/0/0 PTR N-CNU4219HCM. (71) 01:01:12.283041 IP urclouds.50596 > gateway.domain: 62398+ PTR? 205.43.168.192.in-addr.arpa. (45) 01:01:12.289423 IP gateway.domain > urclouds.50596: 62398* 1/0/0 PTR urclouds. (67) 01:01:12.289881 IP urclouds.36334 > gateway.domain: 44220+ PTR? 1.43.168.192.in-addr.arpa. (43) 01:01:12.290163 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 208:400, ack 1, win 269, length 192 01:01:12.290454 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 400, win 547, length 0 01:01:12.353640 IP gateway.domain > urclouds.36334: 44220 NXDomain* 0/1/0 (102) 01:01:12.365928 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 400:1200, ack 1, win 269, length 800 01:01:12.366875 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 1200:1360, ack 1, win 269, length 160 01:01:12.366882 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 1360, win 543, length 0 01:01:12.367229 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 1360:1616, ack 1, win 269, length 256 01:01:12.367467 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 1616:1776, ack 1, win 269, length 160 01:01:12.367703 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 1776, win 542, length 0 15 packets captured 15 packets received by filter 0 packets dropped by kernel [root@urclouds ~]#
How to display all the available Interfaces for tcpdump?
We can use “tcpdump -D” command to display all the available interfaces for tcpdump command. You can see in below output available interfaces on our server.
[root@urclouds ~]# tcpdump -D 1.enp0s3 2.nflog (Linux netfilter log (NFLOG) interface) 3.nfqueue (Linux netfilter queue (NFQUEUE) interface) 4.usbmon1 (USB bus number 1) 5.any (Pseudo-device that captures on all interfaces) 6.lo [Loopback] [root@urclouds ~]#
Packets capturing with human readable timestamp <-tttt option>
By default in tcpdump command output, there is no proper human readable timestamp, if we want to associate human readable timestamp to each captured packet then we can use tcpdump commands with “-tttt” option. Like below.
[root@urclouds ~]# tcpdump -c 10 -tttt -i enp0s3 tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes 2019-10-07 01:29:02.184846 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 1638558757:1638558965, ack 4218648940, win 269, length 208 2019-10-07 01:29:02.185175 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 208, win 544, length 0 2019-10-07 01:29:02.186027 IP urclouds.58817 > gateway.domain: 35292+ PTR? 139.43.168.192.in-addr.arpa. (45) 2019-10-07 01:29:02.268752 IP gateway.domain > urclouds.58817: 35292* 1/0/0 PTR N-CNU4219HCM. (71) 2019-10-07 01:29:02.269140 IP urclouds.54149 > gateway.domain: 21487+ PTR? 205.43.168.192.in-addr.arpa. (45) 2019-10-07 01:29:02.275184 IP gateway.domain > urclouds.54149: 21487* 1/0/0 PTR urclouds. (67) 2019-10-07 01:29:02.275753 IP urclouds.49766 > gateway.domain: 30335+ PTR? 1.43.168.192.in-addr.arpa. (43) 2019-10-07 01:29:02.275986 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 208:512, ack 1, win 269, length 304 2019-10-07 01:29:02.278320 IP gateway.domain > urclouds.49766: 30335 NXDomain 0/0/0 (43) 2019-10-07 01:29:02.280326 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 512:1296, ack 1, win 269, length 784 10 packets captured 11 packets received by filter 0 packets dropped by kernel [root@urclouds ~]#
How to capture and save the packets to a file with <-w option>
We can use tcpdump command with “-w” option to capture and save the file, so that we can analyze those packets in future for further analysis. Like below.
Tcpdump command will be this :- tcpdump -w <file_name.pcap> -i <interface-name>
[root@urclouds ~]# tcpdump -w test.pcap -i enp0s3 tcpdump: listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes ^C7 packets captured 8 packets received by filter 0 packets dropped by kernel [root@urclouds ~]#
You can see in above output we have successfully capture packets in test.pcap. We can verify our test.pcap file is created or not on that path where we have created.
[root@urclouds ~]# ls -l total 8 -rw-------. 1 root root 1408 Oct 5 03:37 anaconda-ks.cfg -rw-r--r--. 1 tcpdump tcpdump 734 Oct 7 01:38 test.pcap [root@urclouds ~]#
You can see in above output we have successfully created test.pcap file on that path.
Read the packets from the saved file with <-r option>
Now we can read our save packets pcap file test.pcap with -r option like below.
[root@urclouds ~]# tcpdump -r test.pcap reading from file test.pcap, link-type EN10MB (Ethernet) 01:38:09.273613 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 1638563621, win 545, length 0 01:38:09.274556 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 1:145, ack 0, win 269, length 144 01:38:09.316082 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 145, win 544, length 0 01:38:13.993981 ARP, Request who-has urclouds (08:00:27:67:18:99 (oui Unknown)) tell N-CNU4219HCM, length 46 01:38:13.994003 ARP, Reply urclouds is-at 08:00:27:67:18:99 (oui Unknown), length 28 01:38:18.179449 ARP, Request who-has N-CNU4219HCM tell gateway, length 46 01:38:21.040565 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [P.], seq 0:64, ack 145, win 544, length 64 [root@urclouds ~]#
You can see in above output we can read our saved test.pcap file with -r option.
Read the packets with human readable timestamp.
[root@urclouds ~]# tcpdump -tttt -r test.pcap reading from file test.pcap, link-type EN10MB (Ethernet) 2019-10-07 01:38:09.273613 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 1638563621, win 545, length 0 2019-10-07 01:38:09.274556 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 1:145, ack 0, win 269, length 144 2019-10-07 01:38:09.316082 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 145, win 544, length 0 2019-10-07 01:38:13.993981 ARP, Request who-has urclouds (08:00:27:67:18:99 (oui Unknown)) tell N-CNU4219HCM, length 46 2019-10-07 01:38:13.994003 ARP, Reply urclouds is-at 08:00:27:67:18:99 (oui Unknown), length 28 2019-10-07 01:38:18.179449 ARP, Request who-has N-CNU4219HCM tell gateway, length 46 2019-10-07 01:38:21.040565 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [P.], seq 0:64, ack 145, win 544, length 64 [root@urclouds ~]#
Try to capture only IP address packets on a specific Interface with <-n option>
We can use -n option in tcpdum command to capture only IP address packets on specific interface. Like below: –
[root@urclouds ~]# tcpdump -n -i enp0s3 tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes 02:01:48.755603 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 1639587365, win 545, length 0 02:01:48.760908 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 1:129, ack 0, win 291, length 128 02:01:48.761258 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 129:481, ack 0, win 291, length 352 02:01:48.761514 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 481, win 543, length 0 02:01:48.761658 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 481:657, ack 0, win 291, length 176 02:01:48.761945 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 657:929, ack 0, win 291, length 272 02:01:48.762208 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 929, win 542, length 0 02:01:48.762339 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 929:1105, ack 0, win 291, length 176 02:01:48.762600 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 1105:1377, ack 0, win 291, length 272 02:01:48.763287 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 1377, win 547, length 0 02:01:48.763844 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 1377:1649, ack 0, win 291, length 272 02:01:48.764041 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 1649:1825, ack 0, win 291, length 176 02:01:48.764250 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 1825, win 545, length 0 02:01:49.043513 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [P.], seq 1120:1184, ack 167297, win 542, length 64 02:01:49.043616 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 167297:167585, ack 1184, win 291, length 288 ^C 1094 packets captured 1094 packets received by filter 0 packets dropped by kernel [root@urclouds ~]#
We can also capture N number of IP address packets using -c and -n option in tcpdump command. Like below: –
[root@urclouds ~]# tcpdump -c 25 -n -i enp0s3 tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes 02:05:04.293051 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 1639757013:1639757221, ack 4218671404, win 291, length 208 02:05:04.293343 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 208, win 546, length 0 02:05:04.293727 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 208:512, ack 1, win 291, length 304 02:05:04.294003 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 512:688, ack 1, win 291, length 176 02:05:04.294215 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 688, win 544, length 0 02:05:04.294460 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 688:960, ack 1, win 291, length 272 02:05:04.294719 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 960:1136, ack 1, win 291, length 176 02:05:04.294826 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 1136, win 542, length 0 02:05:04.295144 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 1136:1408, ack 1, win 291, length 272 02:05:04.295390 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 1408:1584, ack 1, win 291, length 176 02:05:04.295609 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 1584, win 547, length 0 02:05:04.295789 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 1584:1856, ack 1, win 291, length 272 02:05:04.296843 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 1856:2032, ack 1, win 291, length 176 02:05:04.297044 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 2032, win 545, length 0 02:05:04.297243 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 2032:2304, ack 1, win 291, length 272 02:05:04.297463 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 2304:2480, ack 1, win 291, length 176 02:05:04.297655 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 2480, win 544, length 0 02:05:04.297831 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 2480:2752, ack 1, win 291, length 272 02:05:04.298043 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 2752:2928, ack 1, win 291, length 176 02:05:04.298324 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 2928, win 542, length 0 02:05:04.298606 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 2928:3200, ack 1, win 291, length 272 02:05:04.298920 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 3200:3376, ack 1, win 291, length 176 02:05:04.299217 IP 192.168.43.139.57521 > 192.168.43.205.ssh: Flags [.], ack 3376, win 547, length 0 02:05:04.299488 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 3376:3648, ack 1, win 291, length 272 02:05:04.300349 IP 192.168.43.205.ssh > 192.168.43.139.57521: Flags [P.], seq 3648:3824, ack 1, win 291, length 176 25 packets captured 26 packets received by filter 0 packets dropped by kernel [root@urclouds ~]#
Capture only TCP packets on a specific interface
We can also capture TCP packets using tcpdump commands with “tcp” option like below.
[root@urclouds ~]# tcpdump -i enp0s3 tcp tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes 02:15:54.656376 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 1640660485:1640660693, ack 4218678972, win 291, length 208 02:15:54.656849 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 208, win 542, length 0 02:15:54.663873 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 208:496, ack 1, win 291, length 288 02:15:54.664159 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 496:656, ack 1, win 291, length 160 02:15:54.664374 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 656, win 547, length 0 02:15:54.665141 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 656:912, ack 1, win 291, length 256 02:15:54.665563 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 912:1072, ack 1, win 291, length 160 02:15:54.665813 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 1072, win 545, length 0 02:15:54.666087 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 1072:1328, ack 1, win 291, length 256 02:15:54.666377 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 1328:1488, ack 1, win 291, length 160 02:15:54.975276 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 170656, win 545, length 0 02:15:54.975991 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [P.], seq 1121:1185, ack 170656, win 545, length 64 02:15:54.976360 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 170656:170928, ack 1185, win 291, length 272 ^C 1157 packets captured 1157 packets received by filter 0 packets dropped by kernel [root@urclouds ~]#
Capture packets with a specific port on a specific interface
We can capture packet from a specific port like 22 on a specific interface enp0s3 using tcpdump command.
[root@urclouds ~]# tcpdump -i enp0s3 port 22 tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes 02:22:26.431961 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 1641384293, win 543, length 0 02:22:26.435958 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 1:209, ack 0, win 291, length 208 02:22:26.442241 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 209:465, ack 0, win 291, length 256 02:22:26.442456 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 465:625, ack 0, win 291, length 160 02:22:26.442588 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 465, win 547, length 0 02:22:26.442815 IP urclouds.ssh > N-CNU4219HCM.57521: Flags [P.], seq 625:881, ack 0, win 291, length 256 02:22:26.442858 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 881, win 545, length 0 02:22:26.707145 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [.], ack 145761, win 542, length 0 02:22:26.707324 IP N-CNU4219HCM.57521 > urclouds.ssh: Flags [P.], seq 960:1024, ack 145761, win 542, length 64 ^C 987 packets captured 988 packets received by filter 0 packets dropped by kernel [root@urclouds ~]# ^C [root@urclouds ~]#
Packets capturing from Specific Source IP on Specific Interface
We can capture the packets from a specific Source IP using “src” keyword followed by <IP-address> like below.
[root@urclouds ~]# tcpdump -n -i enp0s3 src 192.168.43.205 tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes 17:48:23.978034 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 2274614043:2274614251, ack 1492538122, win 269, length 208 17:48:23.978322 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 208:400, ack 1, win 269, length 192 17:48:23.978423 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 400:576, ack 1, win 269, length 176 17:48:23.978606 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 576:752, ack 1, win 269, length 176 17:48:23.978885 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 752:928, ack 1, win 269, length 176 17:48:23.979066 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 928:1104, ack 1, win 269, length 176 17:48:23.980115 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 1104:1280, ack 1, win 269, length 176 17:48:23.980391 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 1280:1456, ack 1, win 269, length 176 17:48:23.980567 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 1456:1632, ack 1, win 269, length 176 17:48:23.980826 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 1632:1808, ack 1, win 269, length 176 17:48:23.980993 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 1808:1984, ack 1, win 269, length 176 17:48:23.981160 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 1984:2160, ack 1, win 269, length 176 17:48:23.981655 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [.], ack 161, win 269, length 0 17:48:24.280169 IP 192.168.43.205.ssh > 192.168.43.139.57397: Flags [P.], seq 197024:197200, ack 1281, win 269, length 176 ^C 1122 packets captured 1123 packets received by filter 0 packets dropped by kernel [root@urclouds ~]#
Packets capturing from specific destination IP on specific interface
We can also capture tcpdump on destination IP using specific interface like below.
[root@urclouds ~]# tcpdump -n -i enp0s3 dst 192.168.43.139 tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes 18:00:22.613295 IP 192.168.43.205.ssh > 192.168.43.139.57786: Flags [P.], seq 454893203:454893411, ack 1516199003, win 269, length 208 18:00:22.613562 IP 192.168.43.205.ssh > 192.168.43.139.57786: Flags [P.], seq 208:400, ack 1, win 269, length 192 18:00:22.613810 IP 192.168.43.205.ssh > 192.168.43.139.57786: Flags [P.], seq 400:576, ack 1, win 269, length 176 18:00:22.614142 IP 192.168.43.205.ssh > 192.168.43.139.57786: Flags [P.], seq 576:752, ack 1, win 269, length 176 18:00:23.104178 IP 192.168.43.205.ssh > 192.168.43.139.57786: Flags [P.], seq 332032:332208, ack 3521, win 269, length 176 18:00:23.104354 IP 192.168.43.205.ssh > 192.168.43.139.57786: Flags [P.], seq 332208:332384, ack 3521, win 269, length 176 ^C 1895 packets captured 1896 packets received by filter 0 packets dropped by kernel [root@urclouds ~]#
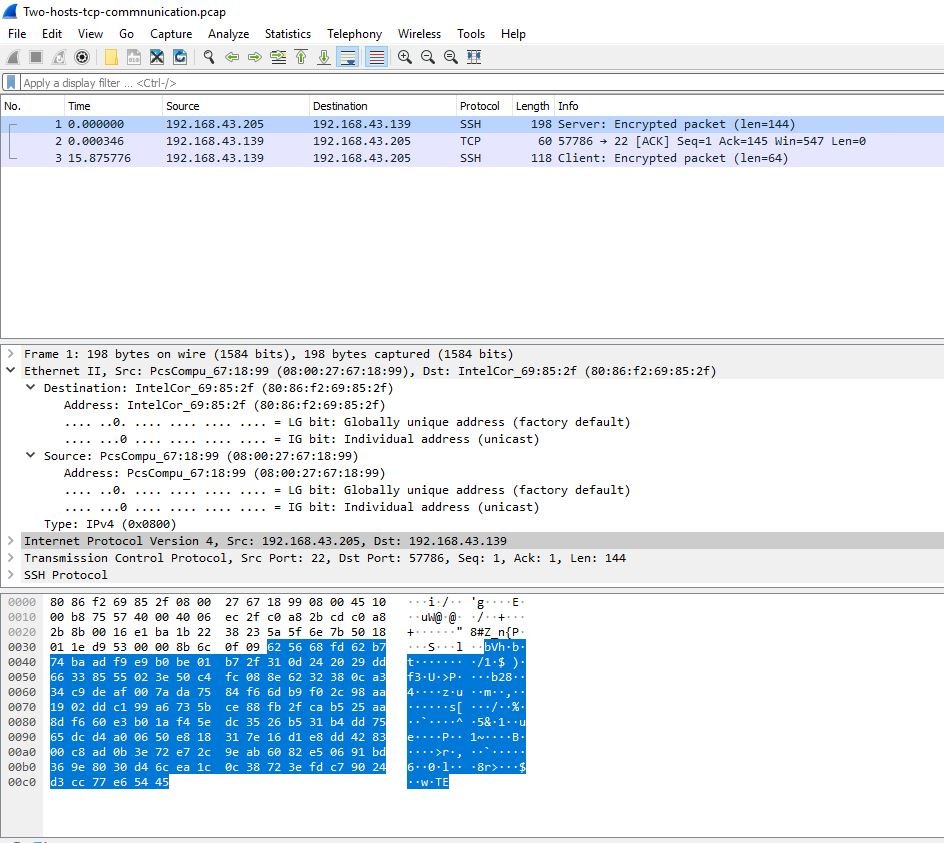
TCP packet communication capturing between two Hosts
Here we will capture TCP packets communication between two hosts. Our first host IP will be 192.168.43.139 and second host IP will be 192.168.43.205 like below.
[root@urclouds ~]# tcpdump -w Two-hosts-tcp-commnunication.pcap -i enp0s3 tcp and (host 192.168.43.139 or host 192.168.43.205) tcpdump: listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes ^C3 packets captured 4 packets received by filter 0 packets dropped by kernel [root@urclouds ~]# ls -l Two-hosts-tcp-commnunication.pcap -rw-r--r--. 1 tcpdump tcpdump 448 Oct 8 18:14 Two-hosts-tcp-commnunication.pcap [root@urclouds ~]#
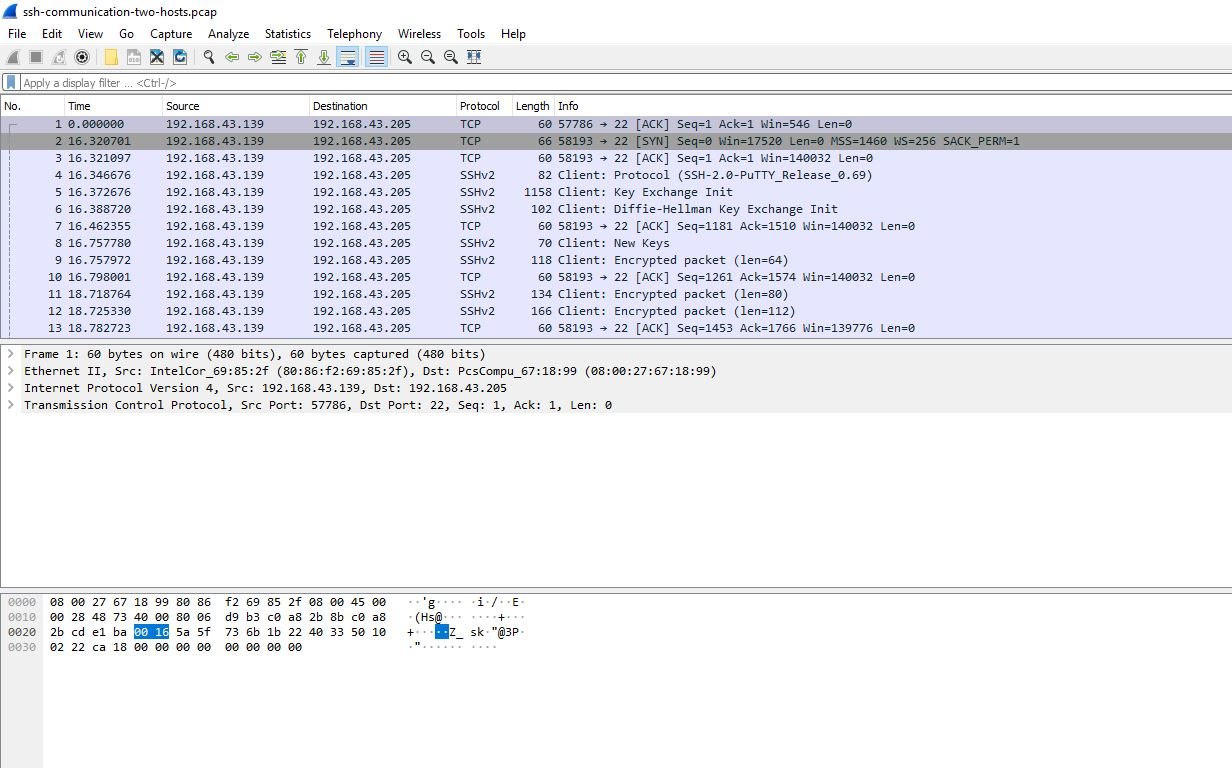
Capture only SSH packet flow between two hosts using tcpdump command.
[root@urclouds ~]# tcpdump -w ssh-communication-two-hosts.pcap -i enp0s3 src 192.168.43.139 and port 22 and dst 192.168.43.205 and port 22 tcpdump: listening on enp0s3, link-type EN10MB (Ethernet), capture size 262144 bytes ^C21 packets captured 21 packets received by filter 0 packets dropped by kernel [root@urclouds ~]# ls -l ssh-communication-two-hosts.pcap -rw-r--r--. 1 tcpdump tcpdump 3630 Oct 8 18:22 ssh-communication-two-hosts.pcap [root@urclouds ~]#
Capture the udp network packets between two hosts
Now I am going to capture udp network packets between two hosts.
[root@urclouds ~]# tcpdump -w two-host-communication.pcap -s 1000 -i enp0s3 udp and (host 192.168.43.139 and host 192.168.43.205) tcpdump: listening on enp0s3, link-type EN10MB (Ethernet), capture size 1000 bytes ^C0 packets captured 0 packets received by filter 0 packets dropped by kernel [root@urclouds ~]#
What’s up to all, how is all, I think every one is getting more from this web page, and your
views are fastidious designed for new people.
The very heart of your writing while sounding reasonable at first, did not work well with me personally after some time. Somewhere within the sentences you actually were able to make me a believer but only for a very short while. I however have a problem with your jumps in logic and one might do nicely to help fill in all those gaps. In the event you can accomplish that, I will certainly be impressed.
Very interesting information!Perfect just what I was looking for!
Reading your article has greatly helped me, and I agree with you. But I still have some questions. Can you help me? I will pay attention to your answer. thank you.
Hey very nice blog!! Man .. Beautiful .. Amazing .. I will bookmark your site and take the feeds also?I’m happy to find numerous useful information here in the post, we need work out more techniques in this regard, thanks for sharing. . . . . .
I may need your help. I tried many ways but couldn’t solve it, but after reading your article, I think you have a way to help me. I’m looking forward for your reply. Thanks.
I’m really enjoying the design and layout of your blog. It’s a very easy on the eyes which makes it much more pleasant for me to come here and visit more often. Did you hire out a designer to create your theme? Great work!
Howdy just wqnted to give you a brief heads up and let you
know a few of thee images aren’t loading correctly.
I’m not sure why but I tyink its a linking issue.
I’ve tried it in two different browsers and both show the
same outcome.
Thank you very much for sharing, I learned a lot from your article. Very cool. Thanks.
I like this post, enjoyed this one thank you for posting. “The goal of revival is conformity to the image of Christ, not imitation of animals.” by Richard F. Lovelace.
Can I replicate your article? Your dedication and expertise are evident, and I’m truly grateful for your contributions.
I would like to thnkx for the efforts you have put in writing this blog. I am hoping the same high-grade blog post from you in the upcoming as well. In fact your creative writing abilities has inspired me to get my own blog now. Really the blogging is spreading its wings quickly. Your write up is a good example of it.
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me.
Woah! I’m really digging the template/theme of this blog.
It’s simple, yet effective. A lot of times it’s difficult to get that “perfect balance” between superb usability and appearance.
I must say you have done a great job with this. In addition,
the blog loads extremely quick for me on Chrome.
Outstanding Blog!
Great blog here! Also your site loads up fast! What host are
you using? Can I get your affiliate link to your host?
I wish my web site loaded up as fast as yours lol
Thank you for the auspicious writeup. It in fact was a amusement account it. Look advanced to far added agreeable from you! However, how can we communicate?